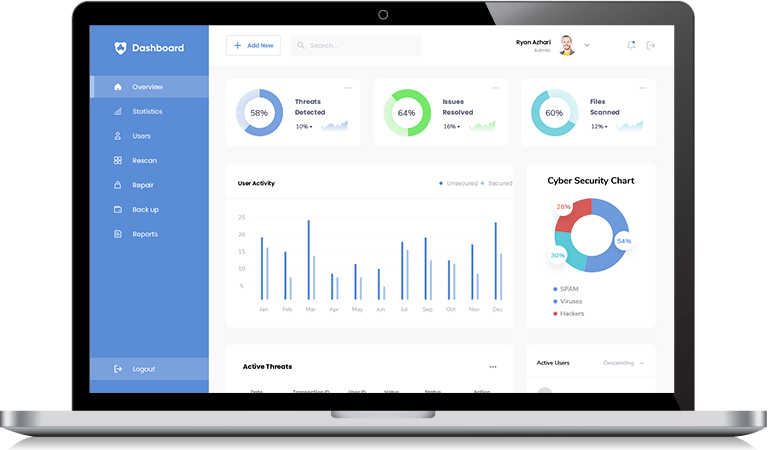
Hire Developers With Cybersecurity Compliance Software Development Experience
Our software developers have many years of hands-on experience designing, engineering, and developing cybersecurity compliance software solutions for healthcare, accounting, payment/banking, and other industries.